How Are Terrorists Using the Internet to Spread Their
Message of Hate? Part 2
By Robert Kaye
 |
| Photo Credit: frazar.net |
Ah, yes, our World Wide Web. Where would most of us be
without it these days? For many of us, it’s difficult to imagine a life without
the interconnectivity and instant interaction of the Internet. The Internet is
a powerful tool that most would agree is now an indispensable part of everyday
life. But this powerful tool is a double-edged sword. Benevolence and crime live side-by-side in the
spaces of the World Wide Web. It provides power to those who are good and those
who are evil. And a new evil has reared its ugly head: Internet Terrorism.
Since its origins and rapid-fire growth starting in the early
1990s, the Internet was heralded as a conduit for an emerging “global village”
where businesses, governments and private citizens could interact with each
other the world over. However, what most people think of as "the Internet" are just
the sites listed in the commercial search engine directories. The Darknet (a.k.a., Deep Web) makes up the
other 98% of the Internet. (I’ll discuss more about this in a subsequent
article in this series).
 |
| Photo Credit: leblogalupus.com |
Over time, the exponential growth of the World Wide Web has
ushered in not only the promise of an interactive medium, but also a sinister
place where criminals ― and yes, terrorists ― do their business and
communications. These are the same terrorist groups you hear and read about in
the news. While they may have different political and/or religious agendas, these
malevolent groups are similar in their desire and ability to use the Internet
to distribute their propaganda, interact with supporters, raise operating
capital, create awareness of and sympathy for their raison d’être (reason to
live), and even to launch operations. Some of this is done on “the normal”
Internet, a lot of it is done on the Darknet.
In our first segment, you may recall I spoke about the
continual threat to the U.S., the West and Israel from militant Islamic terrorists.
I identified some of the major jihadist groups operating today (the U.S. State
Dept. says there are nearly 60 terrorist
organizations across the world). I pointed out some of their major state sponsors
and also discussed how some of them are funded, including theft and usury. (See
Part 1 of our previous blog, “How
Are Terrorist Using the Internet to Spread Their Message of Hate?”) Along
with this segment, subsequent articles will also delve more closely into the
specific ways and means that terrorists use the Internet.
Cyber Jihad
Over the past decade, nearly all active terrorist groups
have established their presence on the Internet and are using it in a multitude
of ways. In addition to setting up their own dedicated websites, they also use
chat rooms, bulletin boards, blogs, forums, video sites, discussion groups and
more. Why use the Internet? Because it’s an easy, affordable method for
disseminating information (and misinformation, when it suits them) across the
world instantly. And ― surprisingly ― a lot of it goes relatively unchecked.
 |
| Photo Credit: dailymail.co.uk |
Case in point: Earlier this week, three young women from Denver, Colorado were arrested in Germany as they were trying to fly
to Syria to join ISIS. Also, a chilling video recently emerged featuring an
Australian who had traveled to Syria to join ISIS. How were these four young
people recruited? The Internet. "ISIS constantly cranks the PR machine, making
expert use of slick videos and social media,” CNN
states in its coverage of these recent headlines. “ISIS' global digital
reach has terror experts in the United States worried about security at home as
well.”
Affirms Gabriel
Weimann PhD, former senior fellow at the United
States Institute of Peace in the introduction to his report entitled “www.terror.net
― How Modern Terrorism Uses the Internet.”:“Today, terrorist organizations and their supporters
maintain hundreds of websites, exploiting the unregulated, anonymous, and
easily accessible nature of the Internet to target an array of messages to a
variety of audiences.”
Dr. Weimann says Internet-based terrorism is “a very dynamic
phenomenon.” Websites can appear suddenly, then alter their formats, then only
to disappear just as rapidly. In some instances, they change their URL or
encrypt it, but still promulgate the same hate-filled content and messages. He
points out the terrorist websites are focused on three main audiences: current
and potential supporters, swaying international public opinion, and enemy
publics.
 |
| Photo Credit: sitelintelgroup.com |
- Easy access
- Little or no regulation, censorship, or other forms of governmental control
- Potentially huge audiences worldwide
- Anonymity of communication
- Rapid flow of information
- Inexpensive development and maintenance of an Internet/web presence
- A multimedia environment (with the ability to combine text, graphics, audio and video and allowing users to download films, songs, books, posters, etc.)
- The ability to manipulate news coverage in the traditional mass media, which increasingly uses the Internet as a source for stories
- The ability to engage in untraceable business transactions and money transfers to help perpetuate their terrorist infrastructure.
 |
| Photo Credit: news.asiantown.net |
Dr. Weimann also authored the book, “Terror
on the Internet.” In a review of that book for the “New YorkTimes’ Sunday
Book Review,” author Robert F. Worth wrote, “Weimann argues that jihadist
groups see the Internet not only as a way to reach followers and recruits, but
as a broader link with mainstream Arab and Muslim populations. In one sickening
example, he describes a Hamas Web Site that is aimed at children, with
cartoon-style graphics, songs and stories.” Welcome to the era of instant inter-generational
e-Hate, Ladies and Gentlemen.
Websites created and managed by terrorist groups are set up
for different reasons and may include their organizational history and
hierarchy; key biographies; speeches; blogs; express their ideological, political
or military aims; issue field reports, maps and news. The fact the Internet has
now become a media-rich environment also means terror groups can post sometimes
graphic photographs and videos of their conquests and celebrated
“achievements,” such as the torture of U.S. soldiers and the recent beheading
of U.S. and U.K. journalists. Certain sites glorify different types of
violence, however other groups may use that as propaganda tool against a rival organization
or a foreign power, against which it’s fighting. Some sites even include gift
shops, where one can buy paraphernalia and by doing so, support the terrorist
groups monetarily.
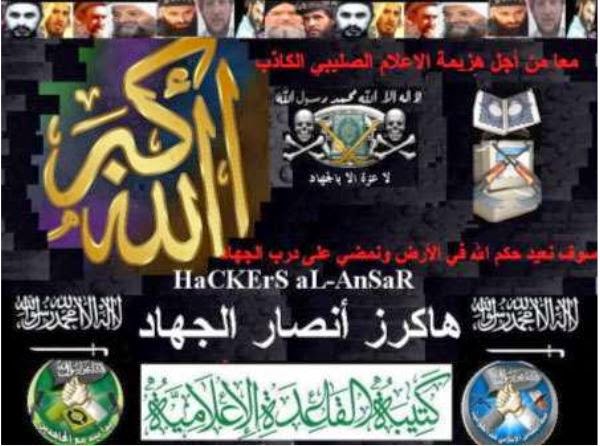
 |
| Photo Credit: rsaconference.com/writable/presentations/file_upload/ht-308_danchev.pdf |
Al-Qaida Hasn’t Been Defeated
 |
| Photo Credit: gaulitics.com |
message boards for planning attacks. Experts took the chatter seriously enough to close down nearly 20 embassies across Africa and Middle East for over a week. The Associated Press reported: “The unspecified call to arms by the al-Qaida leaders, using a multi-layered subterfuge to pass messages from couriers to tech-savvy underlings to attackers, provoked a quick reaction by the U.S. to protect Americans in far-flung corners of the world where the terror network is evolving into regional hubs.
“For years, extremists have used online forums to share
information and drum up support, and over the past decade they have developed
systems that blend encryption programs with anonymity software to hide their
tracks. Jihadist technology may now be so sophisticated and secretive, experts
say, that many communications avoid detection by National Security Agency
programs that were specifically designed to uncover terror plots.”
 |
| Photo Credit: theguardian.com |
 |
| Photo Credit: sitelintelgroup.com |
“Earlier this year,” the article continues, “an
al-Qaida-linked extremist propaganda organization known as the Global Islamic
Media Front released an encrypted instant-messaging system known as ‘Asrar
al-Dardashah,’ or ‘Secrets of the Chat.’ It was a texting version of the
organization's end-to-end encryption program that followers had been using for
years. End-to-end encryption means messages are put into code so that only
senders and receivers can access the content with secure ‘keys.’
“After the NSA programs were revealed in June, jihadi
websites began urging followers to also use software that would hide their
Internet protocol addresses and, essentially, prevent them from being tracked
online. That aimed to add another layer of security to the online traffic.”
Surprisingly, encryption technology, which was once
regulated and overseen by the U.S. for national security reasons, is today a
free-running industry and has been available to the general public since the
1990s. (Say what?!)
Knowledge Base of Operations
 |
| Photo Credit: boomuck.net |
The Internet is also teeming with information that can be
taken advantage of and used by terrorists. Think about it: Readily available
online are maps, satellite photographs (i.e., Google Earth), blueprints and key
information about transportation routes, power and communication grids and
infrastructures, pipeline systems, and dams and water supplies. Also online are explosive device instructions, information about biological
weapons, and even more. After 9/11, the U.S. and other international
governments were in haste to reclassify and delete key information that had previously
been easily accessible online. According to an Associated Press report, the
U.S. government made over one million documents go “404 Page Not Found.”
However, since some of this critical information had already been archived in a
variety of ways, those who had the intent and wherewithal to uncover it could
do so with relative ease ― and, even more disconcerting, may already have.
Furthermore, once these types of documents, diagrams and information are
downloaded, the Internet serves as an ideal environment for sharing such key
data among operatives and like-minded groups that are in collusion with one
another.
A subsequent article in this series will look into detail
about what steps governments, agencies and the military are doing to stop the
proliferation of jihadi websites and terrorists’ Internet use in general.
However, in the meantime, what can you and I do? Several things:
- Be Vigilant – If you come across a suspicious site, or are spammed by one, report it.
 |
| Photo Credit: pamgeller.com |
- Hold Politicians Responsible – Ensure your elected officials are doing all they can to stop terrorism, both online and “on the ground.”
- Educate Yourself – For example, in researching material for this series, I had no idea that terrorists’ use of the Internet was so widespread; nor did I know about the Darknet or its size.
- Share This Series – Forward it to your family, friends and colleagues.
 In this second segment, I began to explore in detail why and
how the Internet has become such a key tool and medium of choice in the arsenal
of jihadist terror organizations. I also discussed some of the ways in
which terrorists have been effectively using it for over a decade. Subsequent segments will continue to
investigate this proliferating practice among jihadist terrorist groups. If you found this article interesting, please
share and forward. If you’d like to leave a comment or question, please do so
in the Comments section below.
In this second segment, I began to explore in detail why and
how the Internet has become such a key tool and medium of choice in the arsenal
of jihadist terror organizations. I also discussed some of the ways in
which terrorists have been effectively using it for over a decade. Subsequent segments will continue to
investigate this proliferating practice among jihadist terrorist groups. If you found this article interesting, please
share and forward. If you’d like to leave a comment or question, please do so
in the Comments section below.
If you'd like a free copy of our eBook, "Internet Marketing Tips for the 21st Century," please fill in the form below and we'll email it to you. Your information is always kept private and is never sold.
Robert Kaye is an internationally published,
multi-award-winning writer and editor.
To date, he’s been published over 450 times in numerous print and
electronic media (Internet, TV, radio, and podcasts) covering a wide variety of
subjects. He currently serves as the Associate Producer for Working the Web to Win.
Related articles











The information in this article (and series) is straight from today's headlines. Relevant, timely, important, and eye-opening. Keep up the good work! More people need to become aware of this issue.
ReplyDeleteExcellent follow-up article to the first one in this series re: Internet terrorism. The subject matter is right out of today's (often disturbing) headlines.
ReplyDeleteThank you for all the useful information. we will change this post with new information. It is a very beautiful post. I appreciate your efforts. Keep posting new updates with us.
ReplyDeleteMindtechAffiliates.com
This article is very interesting. I am very happy that I can read such a valuable article.
ReplyDeleteModern technologies visit