By Carl Weiss
 Big business calls it Data
Mining. Consumers think of it as an
invasion of privacy. Cyber-criminals look
at it as an opportunity to line their pockets.
What it boils down to is the fact that as you surf the web it leaves
digital breadcrumbs that people will scoop up in an effort to make money. If this bothers you, then you need to be
aware of how your browsing habits can be used against you as well as what you
need to do to minimize the electronic trail you leave every time you go online.
Big business calls it Data
Mining. Consumers think of it as an
invasion of privacy. Cyber-criminals look
at it as an opportunity to line their pockets.
What it boils down to is the fact that as you surf the web it leaves
digital breadcrumbs that people will scoop up in an effort to make money. If this bothers you, then you need to be
aware of how your browsing habits can be used against you as well as what you
need to do to minimize the electronic trail you leave every time you go online.What makes these breaches particularly galling is not only the scopes of the penetration, but also the fact that hackers are able to blatantly offer sophisticated hacking tools for sale on the open market. Sources believe that the Target security breach was perpetrated by hackers who used malware purchased from a pair of Russian teens.
The real danger is the fact that not only is credit card information contained in these systems, but also is a tidal wave of other sensitive consumer information. Since data mining has become so endemic and identity theft has become such a problem for so many consumers, the question comes down to whether companies whom collect this information without your consent can be held liable if they are unable to protect it?
There’s Gold in Them There Data Mines
| Data mining (Photo credit: moonhouse) |
Far from being the be-all or
end-all of the equation, the gathering and initial use of this data is only the
tip of a vast submerged iceberg. Because
once this data is accumulated it is then packaged and sold on a worldwide basis
to anyone and everyone willing to pay for it.
Your Data is for Sales, Who’s Buying ?
The NSA, FBI and other
government entities pay for access to mountains of data.
An August 24, 2013 report by
the "Wall Street Journal" stated,
Microsoft, Google, Yahoo
and Facebook all supply user data to the NSA based on secret ordered from the
Foreign Intelligence Surveillance court under a program known as Prism. Although
U.S. law mandates compliance, the government usually helps pay for it.
| Your Data for Sale... (Photo credit: anitakhart) |
A Yahoo spokeswoman referred questions to its Friday
comment in the Guardian. “Federal law requires the US government to reimburse
providers for costs incurred to respond to compulsory legal process imposed by
the government,” the company told the newspaper. “We have requested
reimbursement consistent with this law.”
We’re not talking chump
change here either. More importantly,
who else do these internet edifices share or sell their data with? Well, it all depends on who you ask. Take Google, for instance. While the world’s largest search engine is
tight lipped when it comes to who they share or sell information to, in a 2008
article in the German magazine Stern, the magazine bought a list containing the
names, addresses, dates of birth, occupations and phone numbers of hundreds of
German citizens from the world’s most popular search engine.
The writer of the article
actually picked up the phone and called the phone numbers informing each person
who picked up how and where he had obtained the information. Since Germany has strict laws regarding the
protection of personal data, those who were contacted were outraged as was the
German government, who subsequently sued Google.
Google wasn’t the
only Internet company sued over privacy issues by Germany. So was Facebook, which was dragged into a
lawsuit by German authorities in
2011 over its use of face
recognition software on its services.
Of course, in the United
States there are no such legal speed bumps in the data-mining
superhighway. More to the point, not
only is your personal information available, but what is amazing is the sheer
volume that is being collected. And while search engines and social networks
can be tight lipped when it comes who can use their data, there are other
companies who are quite up front when it comes to selling the personal data of
every man, woman and child in the US.
| MarketingSherpa Email Summit 2006 - Acxiom Digital (Photo credit: MarketingSherpa) |
Here’s some data on Acxiom:
In the third quarter of 2012, Acxiom’s revenue was $281 million, which was down
2% from the same quarter a year before.
For the fiscal year that ended March 31, 2011, Acxiom’s revenue was up
5.5% to $1.16 billion.
“Most people know that basically everything that we do on the Internet is tracked, but data mining
goes far beyond that. When you use a customer rewards card at the
supermarket, the data miners know about it. When you pay for a purchase
with a credit card or a debit card, the data miners know about it. Every
time you buy a prescription drug, that information is sold to someone.
Every time you apply for a loan, a whole host of organizations is
notified. Information has become an extremely valuable commodity, and
thanks to computers and the Internet it is easier to gather information than
ever before.”
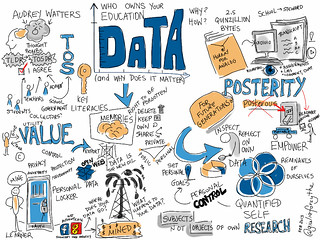
You Don’t Own Your Data, They Do
| #etmooc @audreywatters asks 'Who Owns Your Education Data (and Why Does It Matter?)' (Photo credit: giulia.forsythe) |
The biggest problem for
consumers is that for the most part, they do not own their data. If you subscribe to the majority of social
networks, blogs and portals you need to read the find point in their user
agreements. Because if you do, you will
find out that while you are free to post information on yourself and your
friends, you do not in fact own it. The
operators of the social networks, blogs and portals do.
The only way to be sure, of
who owns what, is to read the user agreements that are part of every browser,
search engine, portal and social network.
But really ... how many of us ever do that? This
is important since the terms of use change from year to year. Google has made a number of sweeping changes
to its privacy issues over the years. In
the current iteration under the heading of “Information We Share” is the
following:
We do not share personal information with
companies, organizations and individuals outside of Google unless one of the
following circumstances applies:
·
With your consent
We will share personal
information with companies, organizations or individuals outside of Google when
we have your consent to do so. We require opt-in consent for the sharing of any sensitive personal information.
·
With domain administrators
If your Google Account is
managed for you by a domain administrator (for
example, for Google Apps users) then your domain administrator and resellers
who provide user support to your organization will have access to your Google
Account information (including your email and other data).
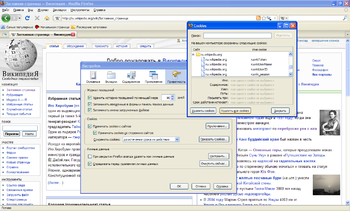
Have a Not-so Sweet Cookie
| English: Cookies settings and view in Firefox 3.0 browser Русский: Просмотр и настройка cookies в браузере Firefox 3.0 (Photo credit: Wikipedia) |
The real elephant in the room
is the fact that for the most part, companies and/or individuals who want to
track your every movement online don’t even have to ask your permission. All they have to do is get you to accept
their cookie. These cookies are not as
sweet as they sound. All they are is a
subroutine that is designed to collect information from your computer, tablet
or Smartphone. The way they get onto
your system is simplicity itself. You
open the door and let them in.
Have you ever downloaded a
“Free App?” Have you ever signed up to
play a “Free Game?” Have you ever
entered a “Free Contest?” If the answer
is yes to any of the above then you may have accepted a cookie onto your system
that is now free to roam and collect as you point and click. Some people have so many of these gizmos on
the loose in their machine that it will slow to a crawl. Sound familiar?
Shaking the Bugs Out of Your Browser
Going incognito doesn't affect the behavior of other people, servers, or software. Be wary of:
- Websites that collect or share information about you
- Internet service providers or employers that track the pages you visit
- Malicious software that tracks your keystrokes in exchange for free smileys
- Surveillance by secret agents
- People standing behind you
When you realize all the many
ways that your personal information can be used by others, the last thing you
want to do is dig a hole from which you cannot hope to escape. Here is a list
of browser plus-in's that can help; Google Privacy, Ad blocker, Ad Block, Ad
Remover, and WOT (Web of Trust). You can find many more by doing a search for
privacy plug-in’s for your browser or going to that browsers store and
searching for them there. You may also find that your antivirus/malware software
also provides plug-in’s for your browsers.
In this article, I discussed how Big Data is changing the way government and big business track
consumer behavior. I discuss how this can lead to huge security breaches since
so much data is housed in one place. I also discuss how this can become a big
problems for these businesses when consumers react negatively to these
breaches. Monetary losses will be huge on both the consumer and business side
and some businesses will not survive these monumental Big Data breaches. Finally,
I have provided several ways that you can minimize browser data tracking, ways to protect
yourself from all the players in the Big Data world. If you found this article
useful, share it with friend and associates. If you have a comment, post it in
the comment sections. Remember this, cookies
are best eaten ... not added to your browser.
If you like this article, you can find more by typing “Internet security” in the search box at the top left of this blog.
If you found this article useful, share it with your friends, families and co-works. If you have a comment related to this article, leave it in the comment sections below.
If you found this article useful, share it with your friends, families and co-works. If you have a comment related to this article, leave it in the comment sections below.
If you'd like a free copy of our eBook, "Internet Marketing Tips for the 21st Century," please fill in the form below and we'll email it to you. Your information is always kept private and is never sold.
Since 1995, Carl Weiss has been helping clients succeed
online. He owns and operates several online marketing businesses,
including Working the Web to
Win and Jacksonville
Video Production. He also co-hosts the weekly radio show, "Working the Web to Win,"
every Tuesday at 4 p.m. Eastern on BlogTalkRadio.com.
Related articles














The era of "Big Brother" has arrived
ReplyDelete